
3 Simple Steps to Arrange DKIM & Enhance E mail Deliverability
DKIM is an e-mail authentication protocol. It capabilities like a digital signature by inserting code within the e-mail header, which then will get encrypted. DKIM gives a manner for mailbox suppliers (MBPs) like Yahoo and Gmail to confirm that an e-mail actually does originate from a licensed consumer of the sending area listed.
This downside has gotten worse in recent times in a big half due to e-mail spoofing. We’ve all been on the receiving finish of this insidious rip-off; once you obtain emails claiming to be from large corporations like PayPal, Amazon, FedEx, or your financial institution, telling you your package deal hasn’t been delivered, or your password has modified, or this bill is unpaid, that’s spoofing. It’s a scammer pretending to be an actual firm, making an attempt to get you to click on on attachments or hand over delicate private info.
DKIM helps defend recipients from scams by permitting mailbox suppliers to distinguish actual senders from pretend ones. It additionally ensures that the e-mail hasn’t been tampered with throughout transmission.
And that is one purpose e-mail supply charges shouldn’t be 100% throughout the board. Some emails ought to be blocked – the illegitimate ones. Your job is to ensure your emails get delivered, and DKIM makes an enormous distinction in serving to that occur.
DKIM originated round 2004 when varied e-mail service know-how corporations started to search for a method to defend e-mail customers from spam. Yahoo created a device referred to as Area Keys and Cisco developed one referred to as Recognized Web Mail.
When these two comparable instruments have been mixed, DKIM was born.
Since then, DKIM has grown in use and recognition as a technique for authenticating emails by verifying the sender is who they declare to be. Listed below are extra historic highlights from the development of DKIM.
In the event you’ve ever despatched emails utilizing an e-mail platform like Mailjet, you recognize that you could write something you need within the ‘From’ area. It’s also possible to create an infinite stream of e-mail addresses to enter because the sending e-mail. However as soon as mailbox suppliers – the Yahoos and Gmails of the world – know and acknowledge PayPal’s digital signature, all of the scammers pretending to be PayPal are straightforward to establish.
DKIM helps mailbox suppliers resolve which emails to dam, which of them to filter into the spam folder, and which of them to ship.
DKIM is much simpler when coupled with DMARC and SPF.
These are literally very totally different. DKIM is nearer to SPF than it’s to DMARC, which we’ll get to in a second. First, what’s SPF? We’re not speaking about sunblock scores right here. SPF stands for “sender coverage framework.” It’s one other e-mail authentication device that lets area homeowners decide which IP addresses can ship emails utilizing that area.
This issues as a result of you’ll be able to solely use DMARC after getting DKIM and SPF arrange.
What’s DMARC? It stands for domain-based message authentication, reporting, and conformance.
The concept behind DMARC is, what occurs if an e-mail fails SPF and DKIM. What ought to Yahoo do? Whereas DKIM is supposed partially to forestall e-mail spoofing, it doesn’t absolutely accomplish that if the mailbox supplier doesn’t block the rip-off emails.
DMARC tells mailbox suppliers what to do if an e-mail fails each of these authentication protocols. For this reason it often will get known as your ‘DMARC coverage.’ It’s what you need incoming mail servers to do if an e-mail fails to move DKIM or SPF.
You may specify considered one of three choices – reject, quarantine, or none.
Reject means simply what it feels like – the e-mail is not going to be delivered and nobody will ever see it. That is what you need if everybody agrees this e-mail is a rip-off.
Quarantine means the recipient received’t get the e-mail, however an administrator can nonetheless see it to allow them to assess the message. You may want this feature to perceive what kinds of threats in opposition to your e-mail fame exist.
None means the message nonetheless will get delivered. While you first begin utilizing DMARC, that is advisable so you’ll be able to see which emails are failing authentication. You don’t wish to immediately have all of them rejected, as a result of if one thing isn’t arrange accurately with DKIM or SPF, your personal official emails may very well be failing authentication. Utilizing none will mean you can repair these issues with out affecting your e-mail deliverability.
The primary purpose you must use DKIM verification is fairly easy: Together with SPF and DMARC, these are the primary e-mail authentication strategies for verifying the id of senders. They’re a number of the simplest methods to forestall phishing and e-mail spoofing, which has severely eroded model belief within the inbox.
However this isn’t DKIM’s solely benefit. In truth, the implementation of those protocols alsoimproves e-mail deliverability by strengthening your e-mail fame with mailbox suppliers and spam blocklists.
Your emails will probably be confirmed as official in your subscribers by their mailbox suppliers, which improves the probabilities of your emails reaching your contacts’ inbox and never the spam folder.
These protocols have change into the usual within the e-mail world. A message despatched with out DKIM and/or SPF could also be thought of suspicious by the totally different e-mail evaluation instruments.
Take a look at our e-book – Touchdown within the inbox: E mail advertising and marketing deliverability fundamentals
Obtain Information
This half can get somewhat difficult, so when you simply wish to get this over with and discover ways to arrange DKIM, you’ll be able to skip to the following part and discover the directions in your working system and DNS supplier.
DKIM is type of like trying to find a hidden treasure. Besides it’s not you doing the searching. It’s the server receiving your emails. The server is in search of a ‘public key’ that can permit it to verify the e-mail sender’s legitimacy.
Establishing DKIM begins with the e-mail sender – that’s you – choosing the e-mail fields you need included in your DKIM signature. This may very well be the topic, physique, from, pre-header, and so forth. You do that as a result of if any of those get altered whereas the e-mail is in transit, even by only a single character, DKIM authentication will fail. You set this up one time. You don’t need to do it each time you ship an e-mail.
Then, once you do ship an e-mail, your e-mail server will generate what’s often called a ‘hash worth,’ which is sort of a coded model of the fields you’ve chosen. This hash worth seems within the e-mail header, and that is what’s known as the e-mail’s DKIM signature.
The hash worth itself will get encrypted with a non-public key, and solely the e-mail sender can entry that key.
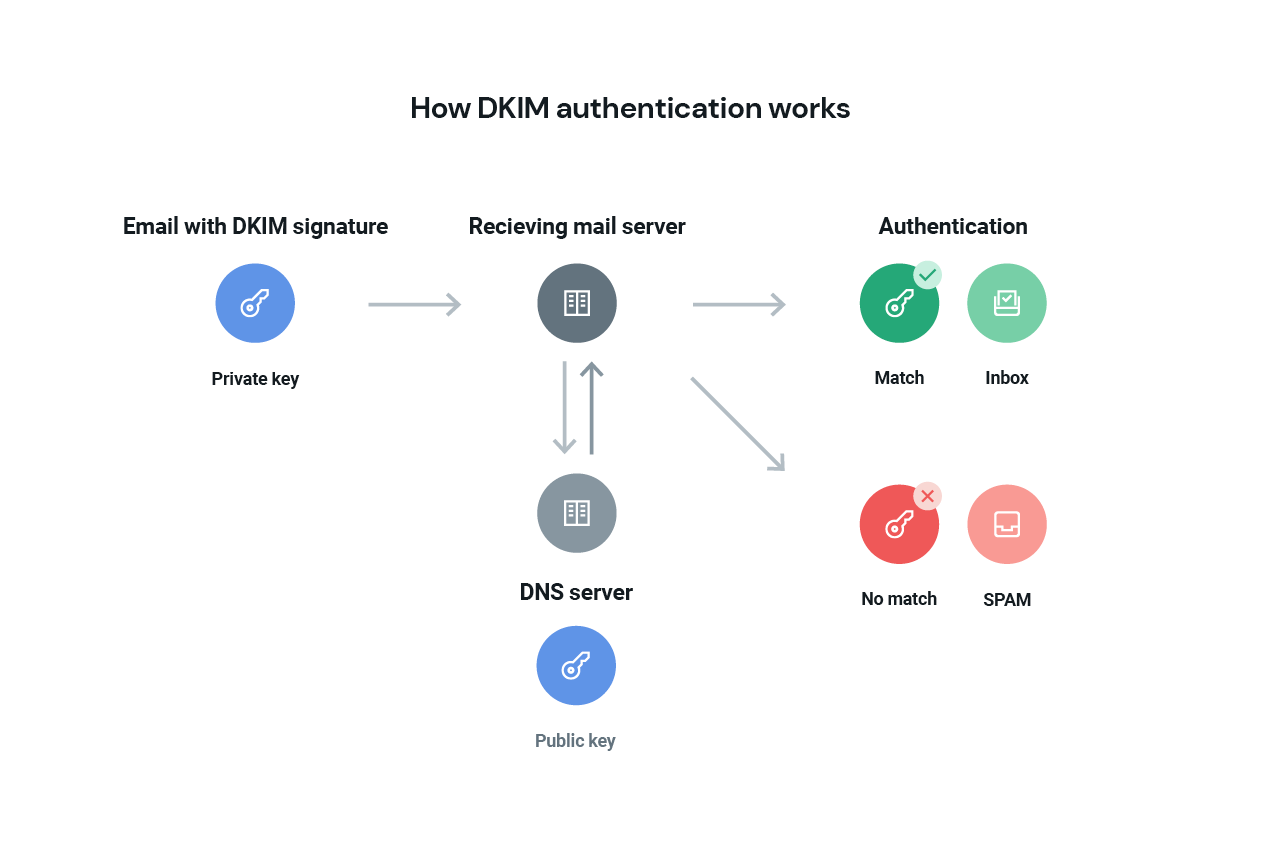
Nonetheless, there’s one other key – the general public key – that the receiving e-mail server can go discover and use to unlock the DKIM signature. That’s the treasure hunt. The place is that this public key? It’s in your DNS, and the receiving e-mail server will search for your public key there. While you arrange DKIM utilizing the directions beneath, you’ll find yourself in your DNS information, and this is the reason.
As soon as the receiving e-mail server finds your public key, it should match the non-public key inside your e-mail header. If it does, this validates the e-mail signature and confirms the legitimacy of the e-mail and the sender. At that time, the hash worth is decrypted, the server can confirm the e-mail hasn’t been altered, and it will get delivered. Take a look at this instance of a DKIM signature.
DKIM keys are available in varied lengths, with 1024-bit and 2048-bit keys being the most typical. The size of the important thing impacts how troublesome it’s for an attacker to crack the encryption. As it’s with normal passwords, the longer the important thing, the tougher it is going to be to interrupt.
Whereas 1024-bit keys is the usual cryptographic size utilized in DKIM e-mail authentication, we extremely advocate shifting to a 2048-bit key. At double the important thing size, 2048-bit keys present considerably stronger encryption and are thought of extra future-proof.
All Sinch Mailjet customers’ sending domains will now default to a 2048-bit DKIM authentication, whereas present authenticated domains (1024-bit) could be up to date to the brand new normal, offering enhanced safety and reliability in opposition to refined e-mail threats.
We’re moving into the weeds a bit right here – the DKIM selector is how the receiving e-mail server finds the DKIM public key. The selector tells the server the place to search out the important thing, and the selector is included as a part of your DKIM signature within the e-mail header.
Need to see your DKIM selector and confirm you may have arrange DKIM accurately?
First, you will discover the selector in your area by sending an e-mail to your self. Open the e-mail and look at the ‘authentic message’, which could be known as the “uncooked message,” or the total header in some e-mail shoppers. You’ll see the e-mail header and might search for the DKIM signature and the s= worth. That’s the DKIM selector.
Then, use your selector worth on this DKIM inspector device to verify that you simply’ve arrange DKIM accurately.
Observe the steps beneath to allow DKIM signing in your e-mail messages:
The device of selection relies on your working system. For Microsoft Home windows you should use PUTTYGen – right here’s a tutorial. For Linux and Mac, you should use ssh-keygen – Github has a wonderful tutorial for this one.
We’ve got offered an inventory of DNS suppliers along with hyperlinks to official and third-party documentation. They might help you with TXT and DNS file setup:
When utilizing open supply SMTP servers like Sendmail or Postfix, or another SMTP server that helps milter, you should use a particular milter ( = e-mail filter), the DKIM milter. This milter has been launched by Sendmail as open supply and lets you signal e-mail headers with a generated non-public DKIM key. For extra info, check out their in depth documentation.
To outline Mailjet as a official sender for e-mail campaigns, you need to configure your SPF information and DKIM information for every of your sending domains.This may solely be performed on customized domains or domains that you simply personal – you received’t be capable of configure DKIM authentication on webmail accounts like Gmail, Hotmail, or Yahoo.
Establishing DKIM with Mailjet could be very easy. Mailjet offers you the general public key to register by means of your web site host interface. There, you’ll be able to combine the general public key into your registration space.
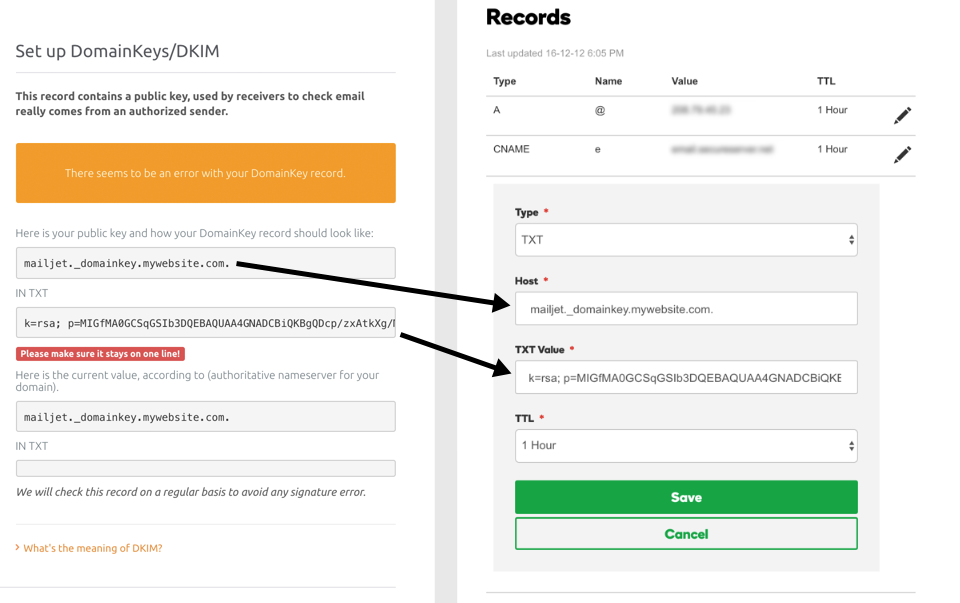
Don’t fear – when you need assistance, you will discover all the required info and step-by-step processes in our documentation. It’s so full, it even consists of help guides for every of the primary internet hosting suppliers (OVH, Gandi, Cloudflare, HostGator and so forth.).
So there you may have it. Hopefully, DKIM doesn’t appear too exhausting to observe anymore.
We now know DKIM is used to validate e-mail senders and to guard your emails in transit. This enables the receiving server to make use of encryption instruments that affirm the authenticity of the sender. You will have all of the instruments and directions to arrange DKIM and make sure that you simply’ve performed it accurately. However you’ll be able to all the time go to the group that laid down the framework –dkim.org – for extra info.
Now that you recognize what DKIM is and how one can implement it, you’ll be able to transfer on to your SPF authentication and make actual progress in enhancing your e-mail deliverability.
Mailjet
Simply create and ship wonderful emails and attain the inbox with Mailjet. Optimize your e-mail advertising and marketing technique and enhance your ROI.
Signal-Up Free
#Simple #Steps #Set #DKIM #Enhance #E mail #Deliverability

