Examine e mail structure and make it safe — Stripo.e mail
To make sure your e mail advertising technique is profitable, it is very important implement the rules of e mail safety and knowledge safety that we mentioned in a earlier article when growing your e mail template design.
On this article, you’ll be taught to what e mail entrepreneurs should take note of shield subscriber knowledge. Another excuse safe design is critical: along with guaranteeing the safety of subscriber knowledge, it immediately impacts e mail deliverability, as e mail shoppers analyze every e mail, so if it appears to be like suspicious or could compromise subscriber knowledge, they ship it to spam and challenge a warning.
Which e mail design components can pose knowledge safety points?
Regarding components in e mail design usually embrace requests for recipient knowledge or the in-depth examine of further data by way of a file or hyperlink. For an e mail marketer, such interactions are important for engagement and acquiring data for segmentation. Nonetheless, attackers can use related blocks to acquire delicate knowledge and unfold viruses.
HTML and JavaScript
Concern: Cybercriminals use Flash, JavaScript, and ActiveX to distribute viruses, which then acquire knowledge, along with prohibited CSS kinds and HTML attributes. Due to this fact, most e mail shoppers don’t assist these applied sciences and are suspicious of emails together with them as a result of they might include susceptible components or could also be used to execute malicious scripts.
Some suggestions for decision-making:
- Watch out to not embrace Flash, JavaScript, or ActiveX in your e mail while you copy code immediately from an internet site.
- Once you use HTML in your emails, comply with the construction of the particular HTML doc. Don’t use probably harmful components, resembling JavaScript, Java applets, ActiveX, VBScript, and IFrames, that are related to exterior CSS or Meta Refresh web sites.
- In case you nonetheless need to add dynamics to your e mail design, exchange Flash animation with a GIF.
Right here is an instance of an e mail with GIF animation:
(Supply: E mail from Pandora)
Hyperlinks
Concern: Attackers use insecure hyperlinks, redirects, or hyperlink shorteners to cover the precise addresses of malicious web sites or .exe file downloads. Due to this fact, e mail shoppers monitor such hyperlinks, and as such, recipients typically don’t belief them and understand them as harmful. This example may happen when click on monitoring is enabled, as a result of the URL will convert to an encrypted hyperlink and thus a mismatch will happen between the URL and the vacation spot.
Some suggestions for determination:
- At all times use hyperlinks to official firm domains. A transparent URL helps customers confirm the authenticity of the hyperlink.
- Don’t use third-party providers (redirectors, hyperlink shorteners) to cover precise details about the touchdown web page.
- Don’t embrace the total URL within the physique of your e mail — as a substitute, insert it as a hyperlink within the textual content or picture.
- The design ought to clearly present the place the hyperlinks lead. For instance, use textual content hyperlinks with clear descriptions as a substitute of “Click on right here.”
(Supply: E mail from StoryBrand)
Attachments
Concern: Cyber criminals ship massive attachments or uncommon file varieties that embrace malicious components or that could be instruments for distributing malware. Concurrently, within the textual content of the e-mail, they move these off as essential, helpful, or fascinating. The e-mail design can thus be used to cover suspicious components or make them seem innocent.
Some suggestions for decision-making:
- Add the file to a internet hosting service and provides the subscriber a hyperlink to the file in an e mail. Under is an instance of how Stripo codecs its obtain hyperlink for a PDF file as a button:

(Supply: E mail from Stripo)
- If it’s good to connect a number of small information, guarantee their dimension doesn’t exceed the allowed restrict for various e mail shoppers, which might vary wherever from 500 KB to five Mb, relying on the consumer to which you might be sending the e-mail.
Photos
Concern: Massive embedded pictures or image-only emails are thought-about harmful, as cybercriminals can use these to put textual content on the picture requesting the recipient present delicate data or take some motion vital for the rip-off to proceed. Sadly, e mail consumer filters can not scan such textual content and can’t warn about such hazard. Because of this, these e mail varieties proactively find yourself in spam.
Some suggestions for decision-making:
- If you wish to use a single picture in your e mail structure, contemplate breaking the picture into a number of elements and putting textual content underneath every picture; steadiness the usage of pictures and textual content to keep away from showing as spam.
- Use suggestions for incorporating embedded pictures in emails from this text.
Have a look at the pattern template beneath, created by a Stripo designer: It seems to be an image-only e mail, nevertheless it really comprises a number of pictures and textual content blocks.
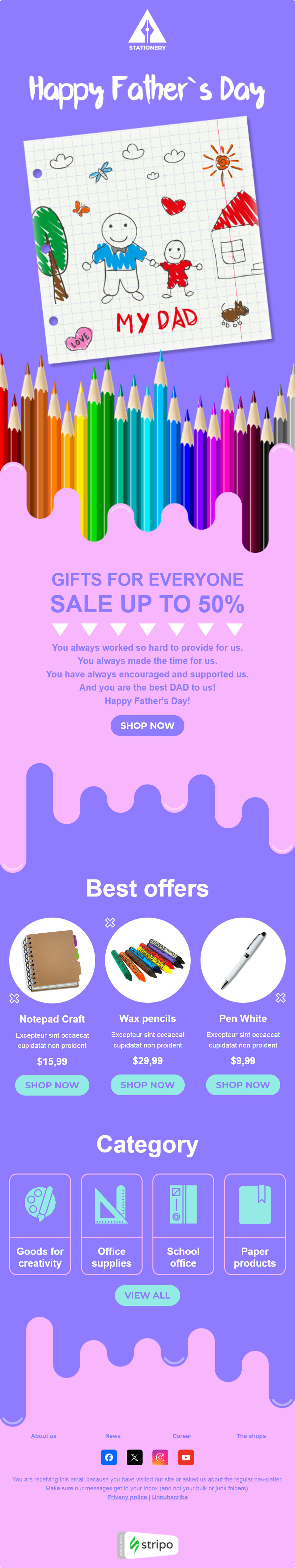
(Supply: Stripo template)
Obfuscated textual content
Concern: Utilizing invisible textual content or textual content that matches the background colour, resembling white textual content on a white background or textual content that blends into the e-mail design, is a typical tactic utilized by spammers and scammers.
Attackers can conceal malicious hyperlinks to keep away from quick detection by customers and safety instruments. Customers could thus unknowingly work together with these hidden components, probably compromising their knowledge.
As well as, obfuscated textual content could also be adopted to show one set of content material to customers whereas the e-mail consumer is processing one other, extra harmful set of directions. This will result in misleading practices the place customers are deceived into offering delicate data or downloading malicious attachments.
Some suggestions for decision-making: To make sure the safety and integrity of emails, keep away from utilizing obfuscated textual content. Then, emails won’t be flagged as suspicious and subscribers might be protected against knowledge breaches.
Monitoring pixels and privateness coverage
Concern: An e mail monitoring pixel is a tiny, invisible device that collects priceless data. It tells you when and the place an e mail was opened and on what gadget. This permits entrepreneurs to learn the way folks work together with their emails to allow them to design their campaigns extra successfully.
Cybercriminals may use monitoring pixels to realize their objectives. A pixel configured by scammers can ship private data to a third-party server, permitting customers to steal private knowledge. Monitoring pixels can be utilized in phishing campaigns, permitting hackers to assemble details about their targets. For instance, if an attacker is aware of that an e mail tackle is legitimate and the e-mail recipient can open the emails, the attacker may exploit such a vulnerability by loading malicious content material into the e-mail.
If a enterprise collects knowledge with out customers’ data and consent, it additionally violates their privateness.
Some suggestions for decision-making:
- Contemplate all knowledge privateness legal guidelines and rules that have an effect on the gathering of consumer habits throughout nations and industries.
- Guarantee transparency concerning knowledge assortment and processing practices and make sure the safety of private knowledge.
- Embrace details about your privateness coverage and knowledge processing within the footer of the e-mail.
- The design should embrace a transparent and easy unsubscribe choice, which can also be a authorized requirement underneath the GDPR and different rules.
Embedded types
Concern: The issue with utilizing embedded types in emails to acquire data is that attackers can simply forge such types, making it tough for recipients to differentiate reliable and fraudulent types. Clicking on these pretend types may spark phishing assaults, malware infections, and knowledge theft.
Additional, subscribers submitting delicate data utilizing such types could also be extra susceptible to interception or unauthorized entry.
Some suggestions for decision-making (when you nonetheless choose to make use of a built-in e mail kind):
- Request solely the info you want. The design of the subscription and knowledge entry kind ought to decrease the quantity of private knowledge requested.
- Use encryption (HTTPS) to transmit knowledge to stop it from being intercepted.
- Use the safe, interactive module “Questionnaire” within the Stripo interactive module generator to create a kind with out coding with ease.
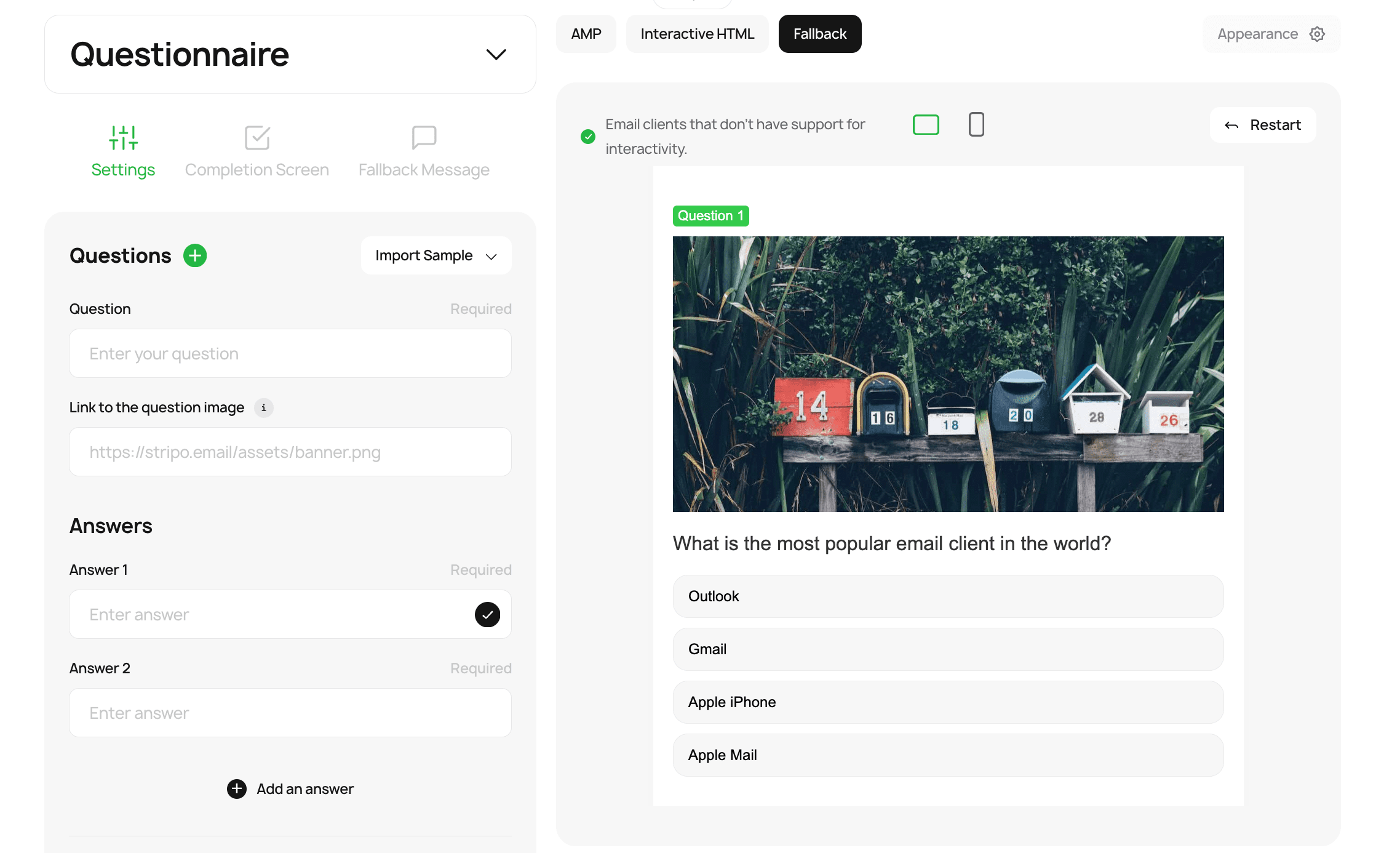
These Stripo types contemplate all the necessities of safe e mail design, and along with AMP and HTML variations, they’ve a fallback, which lets you show an interactive questionnaire to all e mail shoppers and to gather knowledge securely. You even have the chance to trace the effectiveness of those fallbacks — all knowledge are meticulously collected and saved in our Information Service.
Interactive components
Concern: Interactive components in e mail, particularly Accelerated Cell Pages (AMP), are used to create e mail mechanics, resembling carousels, accordions, and totally different types of gamification, however they current safety dangers. Dynamic content material will be manipulated for phishing assaults, permitting customers to work together with malicious types or hyperlinks with out leaving the e-mail consumer.
By verifying AMP emails, Google goals to guard customers from such threats as phishing, malware, and knowledge breaches by checking and blocking each e mail message they deem suspicious.
What e mail shoppers, ESPs, and e mail builders do:
- Solely whitelisted firms are allowed to ship AMP-based emails. Each Gmail and Yahoo rigorously vet every model earlier than including them to their whitelists.
- At any time when Gmail and Verizon resolve whether or not to point out the AMP model of an e mail to recipients, they verify the CORS headers. If the CORS necessities will not be met, a fallback e mail choice is displayed. Nonetheless, AMP content material can’t be redirected.
- For e mail safety, the AMP e mail block has an expiration date. The e-mail consumer stops displaying it after 30 days if the consumer replies or forwards an AMP e mail or when the cache is up to date.
- ESP and e mail builders, in flip, evaluation the code of AMP emails utilizing a velocity restrict. If many requests are despatched from one IP tackle, the system manually checks the contents of such emails.
Some suggestions for decision-making:
- Observe strict guidelines for CORS header settings.
- Use an interactive fallback, then subscribers will all the time see the interactive model of the e-mail.
- Take away unused AMP scripts, and guarantee all sources are loaded solely by HTTPS.
- Use ready-made interactive modules to keep away from errors and risks.
To unravel these issues extra simply, you should utilize the Stripo interactive module generator, which lets you create dynamic content material with zero code-related hustle.
Under is one instance of gamification, the “Discover a Pair” sport, which you’ll create utilizing the interactive module generator:
Extra strategies for better e mail design safety
On this part, you may discover suggestions and techniques that can assist you keep forward of the menace — create e mail designs which might be tough to mimic and that keep subscriber consciousness to make sure their knowledge are stored secure.
Anti-phishing e mail design
E mail design will be a superb weapon within the battle towards phishing assaults and might shield your model from repute hurt and your subscribers from dropping delicate knowledge.
Listed below are a couple of components you’ll be able to incorporate:
- official logos, company colours, and fonts that customers affiliate along with your model in your e mail structure;
- distinctive graphic or design components which might be tough to counterfeit;
- e mail personalization — use the recipient’s title and different personalised data out there solely to you and the consumer;
- e mail signature and phone data;
- the identical format, construction, and tone in every e mail so customers can extra simply acknowledge pretend emails that don’t match the standard communication type;
- cellular optimization and darkish mode — in case your emails look equally good on each desktop and cellular units in gentle and darkish modes, this means a critical angle. Fraudsters hardly ever waste time on such subtleties.
Instructional supplies
Being forewarned is being forearmed — remind subscribers to acknowledge phishing and different knowledge safety threats and shield their knowledge. This method is very related for firms that present delicate consumer knowledge, resembling banks, insurance coverage providers, and so on. They need to educate their subscribers and remind them that they don’t ask for passwords or to realize entry.
A wonderful solution to present assist is by together with in your newsletters details about how customers can report suspicious emails. This may very well be by a devoted e mail tackle or a kind in your web site.
Wrapping up
Guaranteeing the safety of e mail design is essential to defending subscribers from potential threats. Exterior scripts, embedded types, massive attachments, insecure hyperlinks, extreme pictures, and obfuscated textual content can considerably enhance the danger of knowledge breaches and phishing assaults. By eliminating these dangerous components, e mail entrepreneurs can scale back the probabilities of their emails being flagged as harmful and improve the general safety of their communications.
A safe e mail design protects consumer knowledge and builds belief between the model and its subscribers. As such, implementing finest practices in e mail safety helps keep a optimistic repute and ensures that advertising efforts attain the supposed viewers with out being compromised. Finally, prioritizing e mail safety is important to making a secure and reliable e mail surroundings, benefiting the group and its subscribers.
Simply create emails with a safe design, with Stripo
#Examine #e mail #structure #safe #Stripo.e mail